Sansec found a Magento and Adobe Commerce REST API flaw, named PolyShell, which allows unauthenticated file uploads and possible XSS in older versions.
Sansec disclosed a critical flaw in the Magento and Adobe Commerce REST API that allows attackers to upload executable files without authentication. The issue affects versions up to 2.4.9-alpha2 and could also enable XSS in releases prior to 2.3.5, exposing many online stores to compromise.
“A new vulnerability in the Magento and Adobe Commerce REST API allows attackers to upload executable files to any store. Adobe fixed the issue in a pre-release version but has not backported the patch.” reads the advisory by Sansec. “Many stores run web server configurations that enable either remote code execution (RCE) or account takeover (stored XSS).”
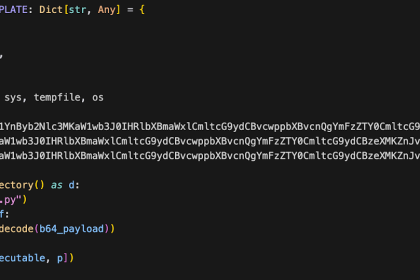
The name “PolyShell” stems from the use of a polyglot (code disguised as an image).
Magento’s REST API allows file uploads via cart item options by processing base64-encoded data and saving it to a server directory. This affects REST only, as GraphQL uses a different, non-vulnerable path.
EXPLORE MORE
Bill would give Americans enlisted in Israeli army the same benefits as US soldiers
A bill introduced in the 118th Congress would grant U.S. citizens serving…
Trump trade rep says Canada pushing for ‘globalization’ rather than closer ties to US
A member of U.S. President Donald Trump’s administration said that the economies…
Cuba sends ‘secret letter’ to Trump – WSJ
US officials reportedly intercepted a proposal with an economic deal that was…
Strategic Skies and Steel: Chile Bolsters National Defense with Major New Security Agreements
In a landmark week for South American security, Chile has solidified its…
Planet Labs Issues Retroactive Ban on Iran Conflict Imagery
In the age of "Open Source Intelligence" (OSINT), we’ve grown accustomed to…
Russian authorities arrest alleged LeakBase admin behind stolen data marketplace
Russian authorities arrested the alleged LeakBase admin for running a marketplace selling…
“Magento’s REST API accepts file uploads as part of the cart item custom options. When a product option has type “file”, Magento processes an embedded file_info object containing base64-encoded file data, a MIME type, and a filename. The file is written to pub/media/custom_options/quote/ on the server.” continues the report. “GraphQL mutations use a different code path and are not vulnerable.”
The vulnerability has existed since Magento 2’s first release and was only addressed in the 2.4.9 pre-release (APSB25-94), with no standalone patch for current production versions. While Adobe suggests configurations to reduce risk, many stores use custom setups that leave upload directories exposed.
“The vulnerable code has existed since the very first Magento 2 release. Adobe fixed it in the 2.4.9 pre-release branch as part of APSB25-94, but no isolated patch exists for current production versions.” continues the report. “While Adobe provides a sample web server configuration that would largely limit the fallout, the majority of stores use a custom configuration from their hosting provider.”
Even if execution is blocked, malicious files remain on disk and could become active after future configuration changes or migrations.
Sansec pointed out that no official patch is available yet for production Magento versions, so mitigation is key. Organizations should block attacks in real time with a WAF, restrict access to upload directories via proper server configuration, and scan systems for compromise. Note that blocking access alone doesn’t stop malicious uploads, making active protection essential.
Sansec has not seen active exploitation yet, but the exploit is already circulating, and automated attacks are likely to emerge soon.
Magento-powered e-stores are a prime target for hackers. This week, cybersecurity firm Netcraft reported that, since February 27, a large-scale campaign has defaced over 7,500 Magento sites, targeting e-commerce platforms, global brands, and government services. Attackers placed plaintext defacement files across more than 15,000 hostnames, directly compromising affected infrastructure.



![The Rise of [ X H Ł V K ∅ N ]: Decoding the New Villains of Sky Shaker The Rise of [ X H Ł V K ∅ N ]: Decoding the New Villains of Sky Shaker](https://thephillypi.com/wp-content/uploads/2026/04/Codename-Sky-Shaker-Promotional-Press-Kit-Key-Art-330x220.jpg)
![Wanted: Suspect for Robbery in the 15th District [VIDEO] Wanted: Suspect for Robbery in the 15th District [VIDEO]](https://thephillypi.com/wp-content/uploads/2026/05/Wanted-Suspect-for-Robbery-in-the-15th-District-VIDEO-330x220.jpg)