U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple, Laravel Livewire and Craft CMS flaws to its Known Exploited Vulnerabilities catalog.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Apple, Laravel Livewire and Craft CMS flaws to its Known Exploited Vulnerabilities (KEV) catalog.
Below are the flaws added to the catalog:
- CVE-2025-31277 (CVSS score of 8.8) Apple Multiple Products Buffer Overflow Vulnerability
- CVE-2025-32432 (CVSS score of 10.0) Craft CMS Code Injection Vulnerability
- CVE-2025-43510 (CVSS score of 7.8) Apple Multiple Products Improper Locking Vulnerability
- CVE-2025-43520 (CVSS score of 8.8) Apple Multiple Products Classic Buffer Overflow Vulnerability
- CVE-2025-54068 (CVSS score of 9.8) Laravel Livewire Code Injection Vulnerability
CISA added the three Apple flaws (CVE-2025-31277, CVE-2025-43510, CVE-2025-43520) in the KEV catalog following reports from recent Google Threat Intelligence Group, iVerify, and Lookout about an iOS exploit kit called DarkSword. The kit targets these vulnerabilities, along with three other bugs, to deliver malware.
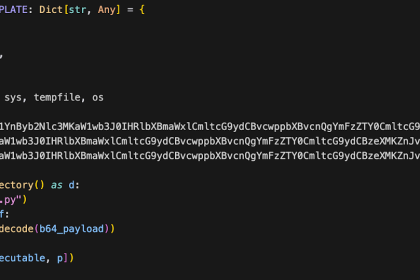
CISA also added a code injection issue, tracked as CVE-2025-32432, to its KeV catalog. In April 2025, Orange Cyberdefense’s CSIRT reported that threat actors exploited two vulnerabilities in Craft CMS to breach servers and steal data. Orange Cyberdefense’s CSIRT warned that threat actors chained two Craft CMS vulnerabilities in attacks in the wild. Orange experts discovered the flaws while investigating a server compromise. The two vulnerabilities, tracked as CVE-2025-32432 and CVE-2024-58136, are respectively a remote code execution (RCE) in Craft CMS and an input validation flaw in the Yii framework used by Craft CMS. According to a report published by SensePost, Orange Cyberdefense’s ethical hacking team, threat actors exploited the two vulnerabilities to breach servers and upload a PHP file manager. The attack began by exploiting the CVE-2025-32432 flaw: a crafted request included a “return URL” that was saved to a PHP session file.
EXPLORE MORE
Why Netanyahu won’t let the Middle East have peace any time soon
Israel is openly considering a new settlement land grab in Lebanon, showing…
CISA and BSI warn orgs of critical PTC Windchill and FlexPLM flaw
CISA warns of a critical flaw in PTC Windchill and FlexPLM (CVE-2026-4681),…
The Rebellion Begins: Taking Down the Realm in ‘Wind Runners’
If you miss the days when space shooters were about reflex-testing "bullet…
Assault in Minneapolis: FBI Opens Investigation into Attack on TPUSA’s Savanah Hernandez
The front lines of American journalism have grown increasingly physical. On Saturday,…
SentinelOne autonomous detection blocks trojaned LiteLLM triggered by Claude Code
SentinelOne AI stopped a LiteLLM supply chain attack in seconds, blocking malicious…
Threat actor UAC-0255 impersonate CERT-UA to spread AGEWHEEZE malware via phishing
Threat actors impersonated CERT-UA to send phishing emails with AGEWHEEZE malware, tricking…
Both vulnerabilities have been fixed; the flaw CVE-2025-32432 has been addressed with the release of versions 3.9.15, 4.14.15, and 5.6.17. The development team behind Yii addressed the issue with the release of Yii 2.0.52 in April. 9th, 2025.
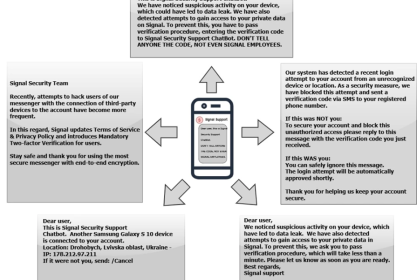
The last vulnerability added to the CISA’s KeV catalog is CVE-2025-54068, which was linked to attacks by Iran-nexus APT MuddyWater, known for targeting diplomatic and critical sectors like energy and finance. The first MuddyWater campaign was observed in late 2017, when the APT group targeted entities in the Middle East.
Experts named the campaign ‘MuddyWater’ due to the difficulty in attributing a wave of attacks between February and October 2017, targeting entities in Saudi Arabia, Iraq, Israel, the United Arab Emirates, Georgia, India, Pakistan, Turkey, and the United States. Over the years, the group has evolved by adding new attack techniques to its arsenal and has also targeted European and North American countries.
The group’s victims are mainly in the telecommunications, government (IT services), and oil sectors.
In January 2022, US Cyber Command (USCYBERCOM) officially linked the MuddyWater APT group to Iran’s Ministry of Intelligence and Security (MOIS).
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.
Experts also recommend that private organizations review the Catalog and address the vulnerabilities in their infrastructure.
CISA orders federal agencies to fix the vulnerabilities by April 3, 2026.