The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds an Aquasecurity Trivy flaw to its Known Exploited Vulnerabilities catalog.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added an Aquasecurity Trivy flaw, tracked as CVE-2026-33634 (CVSS score of 9.3), to its Known Exploited Vulnerabilities (KEV) catalog.
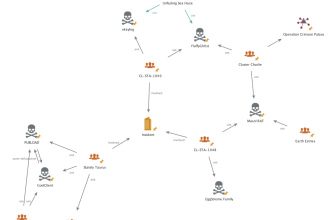
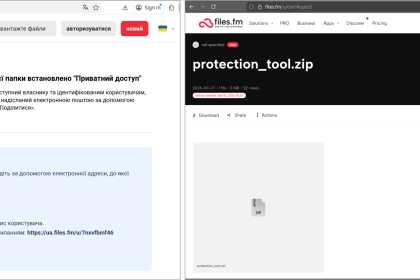
On March 19, 2026, attackers used compromised credentials to release a malicious version of Trivy (v0.69.4) and tamper with related GitHub Actions, turning them into tools for stealing sensitive data. This incident is part of an ongoing supply chain attack that began in late February. Although credentials were rotated after the initial breach, the process was not done simultaneously, likely allowing attackers to retain access and exploit newly generated secrets.
Several components were affected, including Trivy binaries, container images, and GitHub Actions. Safe versions have since been identified, but any system that ran the compromised versions should be treated as exposed.
Organizations are advised to remove affected artifacts, rotate all secrets, and review logs for suspicious activity, especially around March 19–20. To reduce risk, GitHub Actions should always be pinned to immutable commit hashes rather than version tags.
EXPLORE MORE
The White-Collar Collapse: Why the AGI Arrival Means Your Job Is Dying
The window to "prepare" just slammed shut. The era of the comfortable…
Ukraine rocked by new multi-million-dollar corruption scandal
Top management at a state grain corporation and a foreign company colluded…
A Shadow Over the Pulpit: The Disturbing Case of Jonathan Peternel
In a case that has sent shockwaves through both religious and political…
Haifa in the Crosshairs: Iranian Submunitions Strike Israel’s Critical Energy Hub
March 30, 2026 — Dense black smoke is once again clouding the…
Rescue Under Fire: U.S. CSAR Teams Targeted by Ground Fire in High-Stakes Mission Over Iran
KHUZESTAN PROVINCE, IRAN – U.S. combat search-and-rescue (CSAR) teams faced intense hostility…
Missing Juvenile Nevaeh Jones from the 39th District
The Philadelphia Police Department is seeking the public’s assistance in locating a…
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.
Experts also recommend that private organizations review the Catalog and address the vulnerabilities in their infrastructure.
CISA orders federal agencies to fix the vulnerability by April 9, 2026.