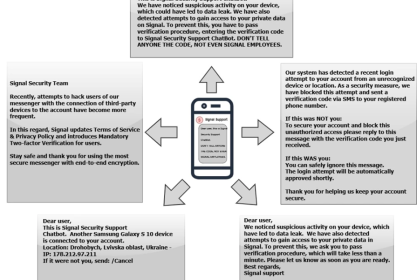
Threat actors impersonated CERT-UA to send phishing emails with AGEWHEEZE malware, tricking victims into installing a fake “security tool.”
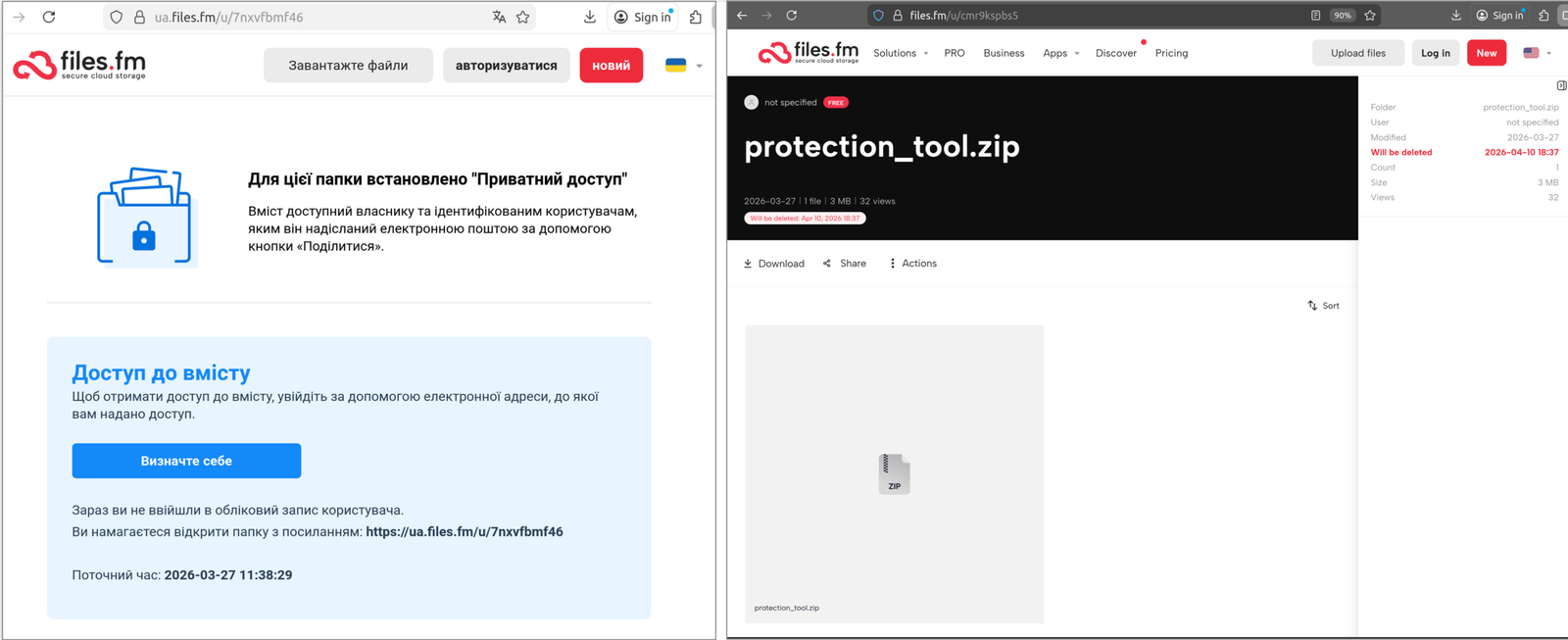
A threat actor, tracked as UAC-0255, impersonated CERT-UA in a phishing campaign, sending emails to about 1 million users. The messages urged victims to download a password-protected archive from Files.fm and install a fake “specialized software,” which actually deployed the AGEWHEEZE remote access tool, giving attackers control over infected systems.
“The National Cyber Incident, Cyber Attack, and Cyber Threat Response Team CERT-UA recorded cases of distribution of emails allegedly on behalf of CERT-UA on March 26-27, 2026, urging people to download a password-protected archive (“CERT_UA_protection_tool.zip”, “protection_tool.zip”) from the Files.fm service and install “specialized software”.” reads the advisory published by CERT-UA. “It was found that the executable file that was offered to be installed (internal package name: “/example.com/tvisor/agent”) is a multifunctional software tool for remote computer control, classified by CERT-UA as AGEWHEEZE.”
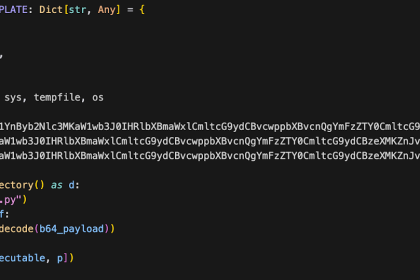
AGEWHEEZE supports command execution, file management, screen capture, input control, and process/service management. It ensures persistence via registry, startup, or scheduled tasks, installing itself in AppData paths. The malware communicates with its server via WebSockets and can also steal clipboard data, run commands, and control system actions.
The campaign targeted government organizations, medical centers, security companies, educational institutions, financial institutions, software development companies, and others.
EXPLORE MORE
U.S. CISA adds Apple, Laravel Livewire and Craft CMS flaws to its Known Exploited Vulnerabilities catalog
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple, Laravel Livewire and…
Philadelphia Police Seek Public’s Help Locating Missing Person 56-Year-Old Alexandra Austin and Vehicle from the 35th District
Philadelphia Police Seek Public's Help Locating Missing Person 56-Year-Old Alexandra Austin and…
U.S. CISA adds a flaw in Google Dawn to its Known Exploited Vulnerabilities catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in…
Dutch Ministry of Finance takes treasury systems offline amid cyber incident investigation
The Dutch Ministry of Finance took treasury banking portal offline after a…
Biological Signaling in the Modern Era: Understanding the Mechanics of Aposematism
In the natural world, survival often depends on the clarity of a…
Ukraine adds Woody Allen to state-linked ‘kill list’
Film star Woody Allen has been added to the list of Ukraine’s…


The attackers created a fake website (cert-ua[.]tech) mimicking the real CERT-UA site to spread the fake “security tool” that is actually AGEWHEEZE malware. The tool allows remote control of infected systems. CERT-UA experts state that the command server is hosted on OVH infrastructure and includes a login page (“The Cult”) with Russian-language elements, suggesting the attackers’ origin or links.
The fake site cert-ua[.]tech includes links to a Telegram channel claiming responsibility for the attack, confirming attribution to UAC-0255.
The fake site was likely AI-generated and included references to “CYBER SERP,” a group active since late 2025, claiming responsibility. The group says it sent phishing emails to 1 million users and infected over 200,000 devices, though this is unverified.
The campaign had a limited impact, infecting only a few devices in educational institutions. CERT-UA experts helped contain it. The case shows how AI can make cyberattacks easier, and highlights the need to reduce attack surfaces and use security tools like AppLocker and system protections.
Authorities thanked Ukrainian telecom providers for supporting cyber defense efforts and sharing threat information. They also warned that AI is making attacks easier, urging organizations to reduce attack surfaces and strengthen security using system protections and dedicated tools.