The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in Cisco FMC and Cisco SCC Firewall Management to its Known Exploited Vulnerabilities catalog.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a flaw in Cisco Secure Firewall Management Center (FMC) Software and Cisco Security Cloud Control (SCC) Firewall Management, tracked as CVE-2026-20131 (CVSS score of 10.0), to its Known Exploited Vulnerabilities (KEV) catalog.
“A vulnerability in the web-based management interface of Cisco Secure Firewall Management Center (FMC) Software could allow an unauthenticated, remote attacker to execute arbitrary Java code as root on an affected device.” reads the advisory. “This vulnerability is due to insecure deserialization of a user-supplied Java byte stream. An attacker could exploit this vulnerability by sending a crafted serialized Java object to the web-based management interface of an affected device. A successful exploit could allow the attacker to execute arbitrary code on the device and elevate privileges to root.”
The vulnerability is a remote code execution flaw that resides in Cisco Secure FMC’s web interface and allows unauthenticated remote attackers to exploit insecure Java deserialization and execute arbitrary code as root by sending a crafted serialized object.
The networking giant addressed the flaw in early March 2026.
EXPLORE MORE
Endangered Missing Person Simon “Abdul” Kioko Jr from the 15th District
Endangered Missing Person Simon "Abdul" Kioko Jr from the 15th District |…
Endangered Missing Person Kira Hunter from the 25th District
Endangered Missing Person Kira Hunter from the 25th District | Philadelphia Police…
Philadelphia Police Seek Public’s Help Locating Missing Person 56-Year-Old Alexandra Austin and Vehicle from the 35th District
Philadelphia Police Seek Public's Help Locating Missing Person 56-Year-Old Alexandra Austin and…
Missing Juvenile Sa’hij Fisher-Burton from the 12th District
Missing Juvenile Sa’hij Fisher-Burton from the 12th District | Philadelphia Police Department…
New House task force set to overhaul handling of sexual misconduct cases
WASHINGTON, D.C. (LifeSiteNews) — Republican Speaker of the House Mike Johnson and…
U.S. CISA adds Apple, Laravel Livewire and Craft CMS flaws to its Known Exploited Vulnerabilities catalog
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple, Laravel Livewire and…
The Interlock ransomware group has been exploiting this critical zero-day RCE vulnerability since late January.
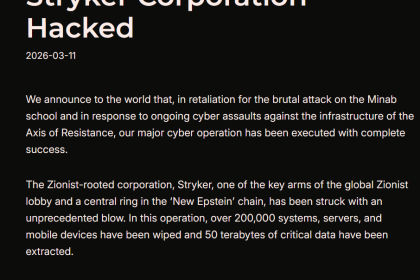
Interlock ransomware group has been active since September 2024, it has targeted multiple organizations, including DaVita, Kettering Health, and Texas Tech University. Recently, researchers observed a new AI-assisted malware strain called Slopoly used in its operations.
Amazon researchers observed the Interlock group exploiting the CVE-2026-20131 flaw 36 days before disclosure, starting on January 26, 2026. This gave attackers time to compromise targets before detection. The activity was uncovered via honeypots and shared with Cisco to aid in the investigation and protect customers.
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.
Experts also recommend that private organizations review the Catalog and address the vulnerabilities in their infrastructure.
CISA orders federal agencies to fix the vulnerability by March 22, 2026.