The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in Langflow to its Known Exploited Vulnerabilities catalog.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a Langflow flaw, tracked as CVE-2026-33017 (CVSS score of 9.3), to its Known Exploited Vulnerabilities (KEV) catalog.
Langflow is a popular tool used for building agentic AI workflows.
CVE-2026-33017 is a critical flaw in Langflow (before v1.9.0) that allows attackers to execute arbitrary code without authentication. The public build endpoint accepts user-supplied data containing Python code, which is executed via exec() without sandboxing. This can lead to full system compromise.
“The POST /api/v1/build_public_tmp/{flow_id}/flow endpoint allows building public flows without requiring authentication. When the optional data parameter is supplied, the endpoint uses attacker-controlled flow data (containing arbitrary Python code in node definitions) instead of the stored flow data from the database. This code is passed to exec() with zero sandboxing, resulting in unauthenticated remote code execution.” reads the advisory. “This is distinct from CVE-2025-3248, which fixed /api/v1/validate/code by adding authentication. The build_public_tmp endpoint is designed to be unauthenticated (for public flows) but incorrectly accepts attacker-supplied flow data containing arbitrary executable code.”
EXPLORE MORE
Open letter to MPs demands changes to Liberal internet bill
OTTAWA (LifeSiteNews) — A collective of Canadian lawyers and top academics demanded…
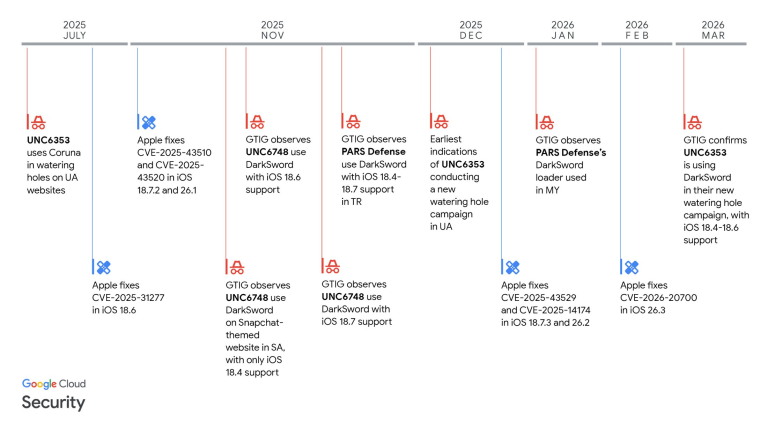
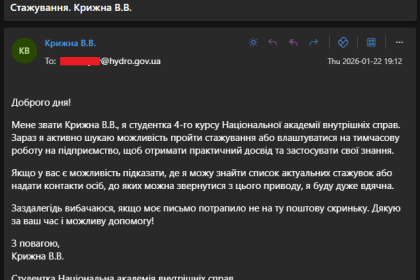
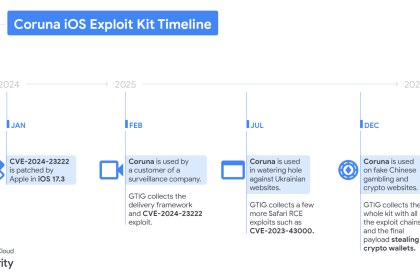
DarkSword emerges as powerful iOS exploit tool in global attacks
DarkSword, a new iOS exploit kit, is used by multiple actors to…
Missing Juvenile Jeffrey Callands from the 14th District
The Philadelphia Police Department’s Northwest Detective Division is requesting the public’s help…
Cuba sends ‘secret letter’ to Trump – WSJ
US officials reportedly intercepted a proposal with an economic deal that was…
Revenge of the Neanderthal by Willis A. Carto
The article "Revenge of the Neanderthal," authored by Willis A. Carto and…
Italy’s L’Espresso Cover Sparks Israeli Diplomatic Row
In the world of independent publishing, we often say that the truth…
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.
Experts also recommend that private organizations review the Catalog and address the vulnerabilities in their infrastructure.
CISA orders federal agencies to fix the vulnerability by April 8, 2026.
In May 2025, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added another Langflow flaw, tracked as CVE-2025-3248 (CVSS score of 9.8), to its Known Exploited Vulnerabilities (KEV) catalog.
CVE-2025-3248 is a code injection vulnerability in the /api/v1/validate/code endpoint. A remote, unauthenticated attacker can exploit it by sending crafted HTTP requests to execute arbitrary code. The flaw impacts versions prior to 1.3.0.
Researchers from cybersecurity firm Horizon3.ai discovered the vulnerability and pointed out that it is easily exploitable.