A new AITM phishing campaign targets TikTok Business accounts to hijack them for malvertising, continuing tactics seen in earlier Google-themed scams.
Push Security researchers uncovered a new wave of AITM phishing pages targeting TikTok for Business accounts, aiming to hijack them for malvertising. The campaign includes TikTok and Google-themed fake pages, showing links to previous operations. Once compromised, accounts are used to run malicious ads, steal credentials, spread malware, and conduct ad fraud, diverting company advertising budgets for profit.
Attackers used newly registered domains created within seconds and hosted behind Cloudflare. The pages follow a common naming pattern and redirect victims from legitimate services before loading fake TikTok for Business or Google “Schedule a call” pages.

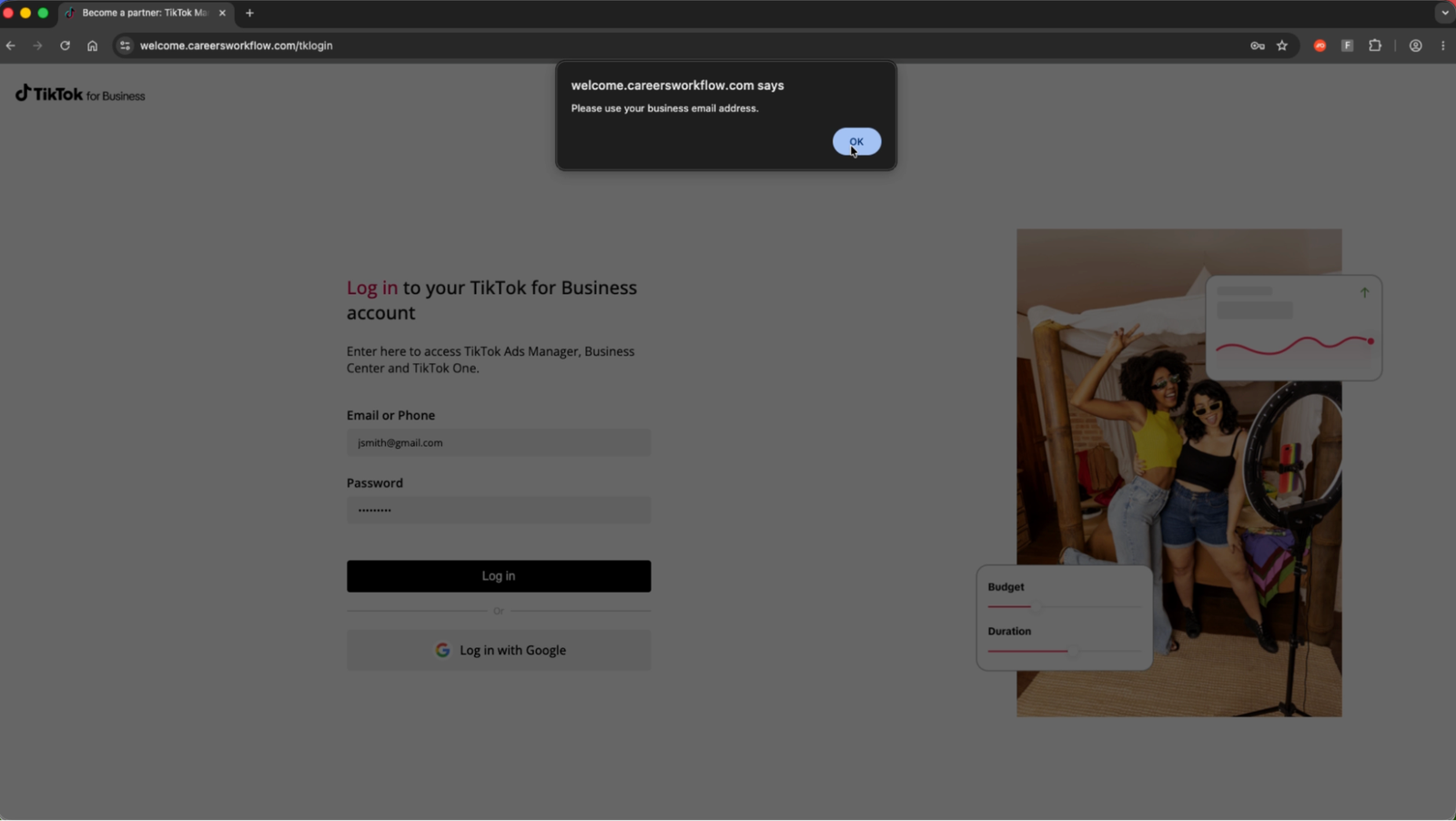
Users are asked to fill in basic details, then shown a malicious login page powered by an AITM phishing kit. The campaign uses bot protection to evade detection and likely spreads via targeted emails, similar to past operations.
“When the link is first clicked, the page is silently redirected from a legitimate Google Storage site before loading the page.” reads the report published by Push Security. “A Cloudflare Turnstile check is used to prevent security bots from analyzing the page, before loading either a TikTok or Google themed page. Progressing through the forms ultimately serves up an AITM phishing page.”
EXPLORE MORE
Robot Wars over Iraq: U.S. ‘Coyote’ Drone Smashes Iranian Kamikaze in Mid-Air
The skies over Erbil, Iraq, looked like a scene from a sci-fi…
Indianapolis: Councilor’s Home Targeted with Gunfire Over Data Center Dispute
A neighborhood dispute over technological infrastructure took a violent and "deeply unsettling"…
Rescue Under Fire: U.S. CSAR Teams Targeted by Ground Fire in High-Stakes Mission Over Iran
KHUZESTAN PROVINCE, IRAN – U.S. combat search-and-rescue (CSAR) teams faced intense hostility…
The “Madman” and the Resignation: General Randy George’s Abrupt Exit from the Pentagon
The Pentagon is currently a house of cards in a windstorm. In…
The Isfahan Incursion: Inside the Most Daring U.S. Special Ops Rescue Since “Eagle Claw”
The mountains of southern Iran just played host to a military operation…
Google links Axios npm supply chain attack to North Korea-linked APT UNC1069
Google links the Axios npm supply chain attack to North Korean threat…

By combining trusted branding, redirects, and layered deception, attackers increase success rates and harvest credentials for further abuse, including account takeover and fraud.
While phishing campaigns usually mimic platforms like Google or Microsoft, targeting TikTok is becoming more common.
The platform has long been used to spread malicious links and social engineering content, including videos that trick users into installing infostealers like Vidar or StealC. It is also widely abused for crypto scams and direct attacks via messages. Gaining access to TikTok business accounts is especially valuable, as they can be used for malvertising and fraud.
Many users log in via Google, meaning a single compromise can expose both TikTok and Google accounts, enabling broader abuse such as ad fraud, data theft, and access to other connected services.
The report also includes Indicators of Compromise (IoCs) for this campaign.
“Short-lived IoCs are of limited value when tackling modern phishing attacks due to the rate at which attackers are able to quickly spin up and rotate the sites used in the attack chain, often dynamically serving different URLs to site visitors.” concludes the report.